Update: Directly from Daniel Cuthbert himself.
Your posting needs to be updated to reflect current UK, and possibly future European, laws.
Testing ANY website without authorisation is illegal in the uk. Under the Computer Misuse Act of 1990, it states "It is an offense to make a computer perform a function and for that function to be deemed unauthorised by the owner of that computer". Simply put, by doing a simple GET on the site could be deemed illegal if the owner didnt want you to do that. Testing for XSS is a punishable offense and people will, and have, been charged with this in the UK.
Wow. This is a seriously broad definition, dangerously so. Thanks for the Daniel. I wonder how often this law is actually being used to prosecute. Coicidentially I there was another post on the legality of penetration testing today on SF pen-test, this time from Germany.
"in Germany we are about to implement the cybercrime treaty in local law with the number § 202 c. This change will make the possession, trafficking, making available and producing of tools with the *intention* for hacking and snooping traffic an offense punishable with up to a year in prison."
This might actually be helping the bad guys more than the good guys and also has implications for companies who run businesses making these tools (Even the big guys). Then I went and looked up the U.S. Computer Fraud and Abuse Act (via) wikipedia. According to the 6 items listed that are against the law, they all seems to have the qualifier of "intent to defraud". This wording seems saner to me.
------
RSnake’s message board sla.ckers.org has been on fire with cross-site scripting vulnerability disclosures. There has been intense media coverage from Dark Reading, InfoWorld, TechWorld, syndication to Dr. Dobb’s, and even a Slashdot’ing for good measure. We all know XSS is a huge problem, a problem likely to get worse, but one issue that hasn’t been raised is legality. On what side of the law do you land when disclosing proof-of-concept (PoC) that a website is vulnerable to XSS? This is particularly important in light of the recent hacking conviction stories of Eric McCarty (SQL Injection) and Daniel Cuthbert (Directory Traversal). I’m no lawyer, but here’s my take.
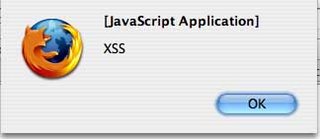
We know penetration testing a website without consent is unethical and possibly illegal. Gaining access to sensitive information is clearly crossing the line. This is where XSS is different. Testing websites for XSS has nominal impact and does not require actual exploitation of anything. There is no legit reason to go after names, addresses, cookies, credit card numbers, attack users, create worms, etc. Exploitation PoC MAY be required in the case of SQL Injection or Directory Traversal, but certainly not XSS. Creating an XSS PoC link displaying a JavaScript alert box is harmless and all you really need. If you used the hole to launch an XSS-Phishing Scam, that’s cut and dry illegal in my book.
Would this rational keep you on the safe side of the law? I think so, hope so, but I certainly don’t know so. My bet is in the next 12 months we'll find out.
4 comments:
Thanks for referencing me :)
Just for info sakes, if they are testing ANY website based in the UK, it is illegal.
The current Computer Misuse Act makes it a offense if the computer is made to perform a function and that function is deemed unauthorised by the owner of that computer.
Simply put: you enter a XSS and the owner doesnt like it, your screwed.
And for the record, my "directory traversal" was actually using ../../ in the browser rather than the back button.
This is terribly generic. I would think non-persistent XSS would be difficult to hold up in court.
In this situation, would the computer used "to perform a function..deemed unauthorised" be the server software or the client software?
I would imagine this point could be argued... then again...
What about phishing then ?
Michael receives a email, the content (html) is : "click here to visit our fantastic website".
Michael doesn't know it, but the address under the link contains a XSS string.
When Michael clicks on the link, the 'fantastic website' is attacked.
Is Michael a criminal because he is ignorant about the situation ?
So good topic really i like any post talking about Investment Plans but i want to say thing to u Investing not that only ... you can see in Investment The Nature of Externalities and more , you shall search in Google and Wikipedia about that .... thanks a gain ,,,
Post a Comment